Deliver Your
Content
Forward
We provide reliable content delivery wherever you need it. With us, you get precision, speed, and confidence at every step.


Global Network
300+
Edge Nodes
Uptime SLA
99.99%
Guaranteed
Avg Response
12ms
Globally
/Services
Tailored
Solutions
We offer a comprehensive range of services designed to meet the diverse needs of businesses. From edge caching to encrypted delivery, every solution is built for scale.
/Approach
Built different from the
ground up
Ingest
Your content enters our pipeline through a single API call. We handle validation, optimization, and replication automatically.
Distribute
Intelligent routing pushes assets to edge nodes closest to your users. No cold starts, no cache misses, no waiting.
Deliver
Signed, encrypted, rate-limited. Every download is authenticated and logged. Your content stays yours.
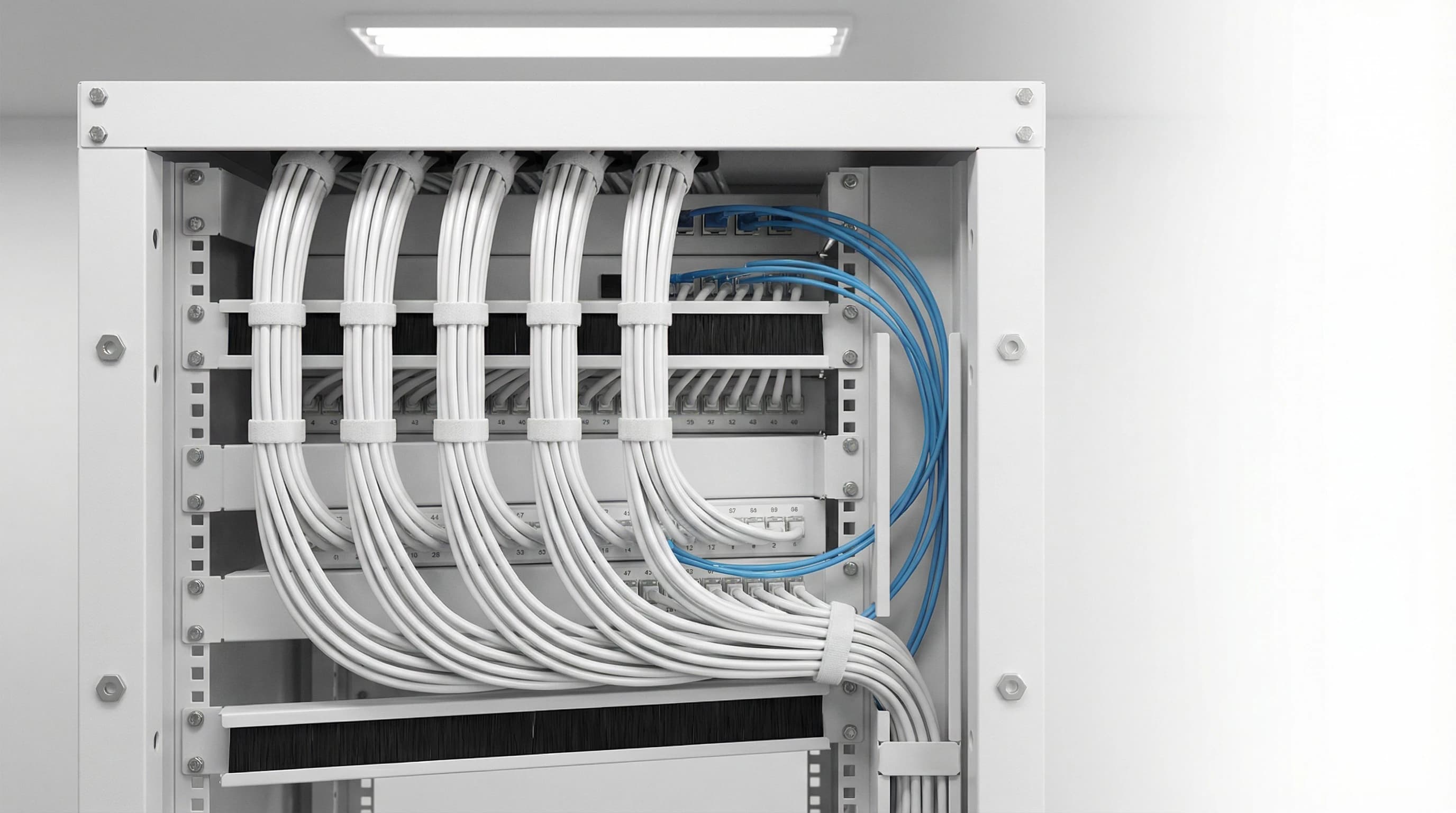
/Infrastructure
Every file passes through
three layers
of verification
HMAC signature validation. One-time token consumption. Active subscription re-verification. Nothing reaches the end user without passing all three.
Learn more




